What are DMARC, DKIM, and SPF in email lifecycle?
Article about DMARC, DKIM, and SPF records
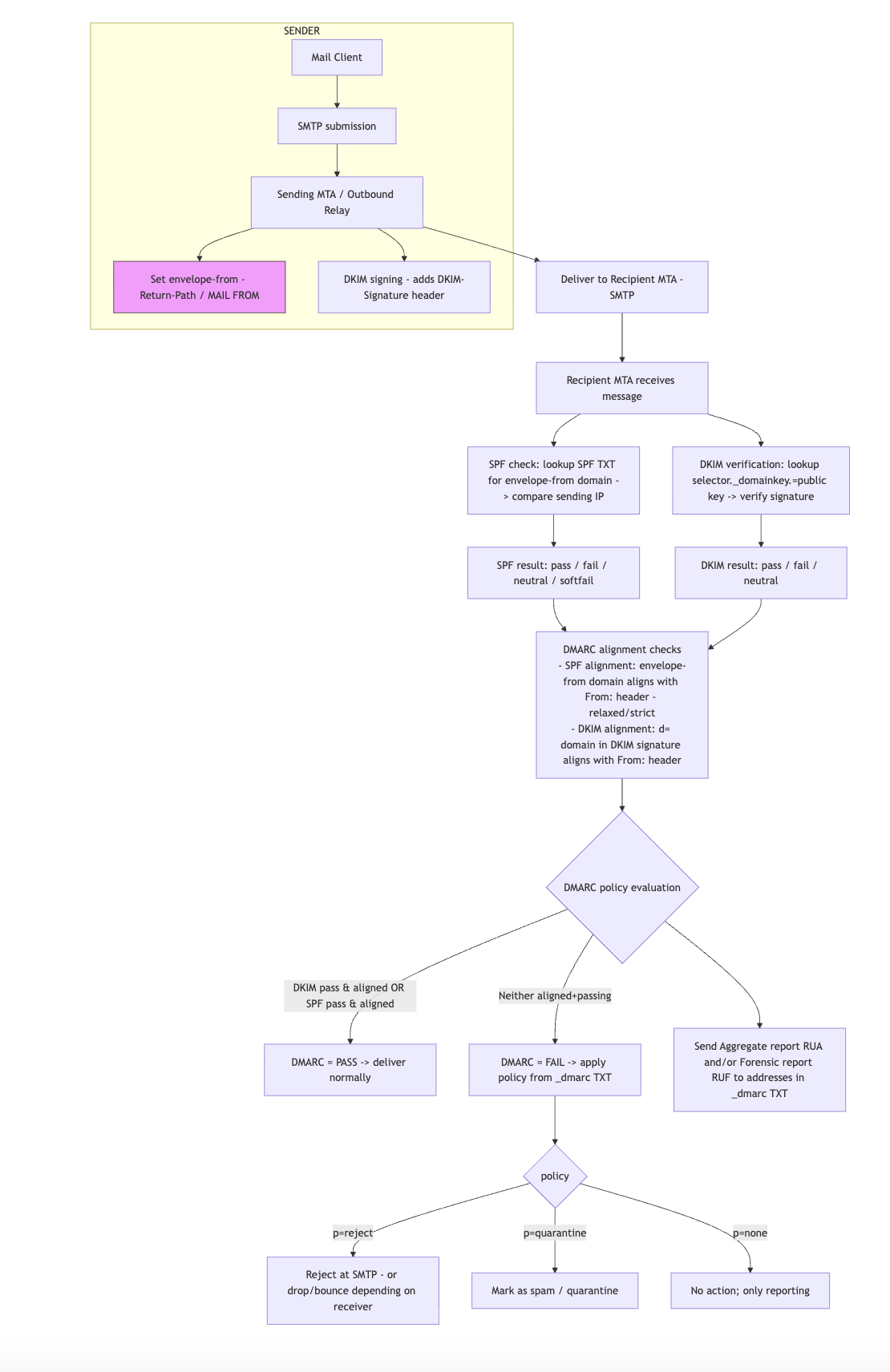
DMARC, DKIM, and SPF are three email authentication methods. Together, they help prevent spammers, phishers, and other unauthorized parties from sending emails on behalf of a domain* they do not own.
DKIM and SPF can be compared to a business license or a doctor's medical degree displayed on the wall of an office — they help demonstrate legitimacy.
Meanwhile, DMARC tells mail servers what to do when DKIM or SPF fail, whether that is marking the failing emails as "spam", delivering the emails anyway, or dropping the emails altogether.
Domains that have not set up SPF, DKIM, and DMARC correctly may find that their emails get quarantined as spam, or are not delivered to their recipients. They are also in danger of having spammers impersonate them.
Source: What are DMARC, DKIM, and SPF? | Cloudflare
1. SPF (Sender Policy Framework)
Who configures it? → Sender’s side (the domain owner publishes an SPF record in DNS).
Who uses it? → Receiver’s side (the recipient’s mail server checks if the sending IP is authorized in the SPF record of the sender’s domain).
Purpose: Prevents unauthorised mail servers from sending on behalf of your domain.
2. DKIM (DomainKeys Identified Mail)
Who configures it? → Sender’s side (the domain owner generates a private key to sign emails, and publishes the public key in DNS).
Who uses it? → Receiver’s side (the recipient’s mail server uses the public key from DNS to verify that the email wasn’t tampered with and that it was signed by the sending domain).
Purpose: Ensures the message content hasn’t been altered and ties the message cryptographically to the sender’s domain.
3. DMARC (Domain-based Message Authentication, Reporting & Conformance)
Who configures it? → Sender’s side (the domain owner publishes a DMARC policy in DNS).
Who uses it? → Receiver’s side (recipient mail server checks SPF + DKIM results, verifies domain alignment, then enforces the sender’s DMARC policy: none, quarantine, or reject).
Purpose: Tells the receiver what to do if SPF/DKIM fails and provides feedback reports to the domain owner.
✅ Summary:
Sender → Publishes SPF, DKIM, DMARC DNS records & signs emails (for DKIM).
Receiver → Performs the actual SPF, DKIM, DMARC checks when an email arrives.
FAQs | What happens when?
1. When SPF Alignment Fails
If SPF fails alignment, it means the domain in the MAIL FROM (envelope_from) does not match the domain in From: header (per DMARC rules).
DMARC doesn’t stop at SPF — it checks either SPF or DKIM (and their alignment).
If DKIM passes and aligns, then DMARC still passes (so no action taken).
If both SPF and DKIM fail alignment, then DMARC fails.
2. When DMARC Policy = quarantine
If DMARC fails (both SPF & DKIM misaligned):
Receiving server is instructed to treat the mail as suspicious.
Common behaviors:
Place into Spam/Junk folder.
Apply warnings like “This message may be forged.”
The mail is not outright rejected at SMTP, it just doesn’t land in the inbox.
3. When DMARC Policy = reject
If DMARC fails:
The receiving server is instructed to reject the email during SMTP transaction.
The mail never reaches the recipient’s mailbox (not even spam).
Depending on server config, sender may get an NDR (bounce message) like “550 5.7.1 Unauthenticated mail from X is not accepted”.
🔑 Key Point
One aligned pass (SPF or DKIM) = DMARC pass
Both fail = DMARC fail → action depends on policy (none, quarantine, or reject)
